The feature is that the daemon listens for commands that tell it to do things like scan files. Normally, it listens only locally for such commands, but can be reconfigured to listen remotely on TCP port 3310. Some packages that include ClamAV sometimes default to this.
It's a simple protocol that consists of sending a command in clear text, like "PING", "VERSION", "SHUTDOWN", or "SCAN
So I ran masscan with the following command:
masscan 0.0.0.0/0 -p3310 --banners --hello-string[3310] VkVSU0lPTg==Normally when you scan an address range (/0) and port (3310), you'd just see which ports are open/closed. That's not useful in this case, because it finds 2.7 million machines. Instead, you want to establish a full TCP connection. That's what the --banners option does, giving us only 38 thousand machines that successfully establish a connection. The remaining machines are large ranges on the Internet where firewalls are configured to respond with SYN-ACK, with the express purpose of frustrating port scanners.
But of those 38k machines, most are actually things like web servers running on odd ports. 51 machines running VNC, 641 machines running SSH, and so on.
To find specifically ClamAV, I send a command using the --hello-string feature. I send the text "VERSION", which must be encoded with base64 on the command-line for masscan (in case you need to also send binary).
This finds 5950 machines (i.e. 6k) that respond back with a ClamAV signature. typical examples of this response are:
At first I thought the date was when they last updated the software, maybe as a page. Roughly half had dates of either this morning or the day before. But no, it's actually the dates when they last updated their signatures.
From this we can conclude that roughly half of ClamAV installations are configured to auto-update their signatures.
Roughly 2400 machines (nearly half) had the version 0.97.5. This was released in June 2012 (four years old). I'm thinking some appliance maker like Barracuda bundled the software -- appliances are notorious for not getting updated software. That hints at why this non-default configuration is so common -- it's not users who made this decision, but the software that bundles ClamAV with other things. Scanning other ports gives me no clues -- they appear all over the map, with different versions of SSH, different services running, different SSL versions, and so on. I thought maybe "mail server" (since that'd be a common task for ClamAV), but there were only a few servers, and they ran different mail server software. So it's a mystery why this specific version is so popular.
I manually tested various machines with "SCAN foo". They all replied "file not found", which hints that all the units I found are vulnerable to this 0day.
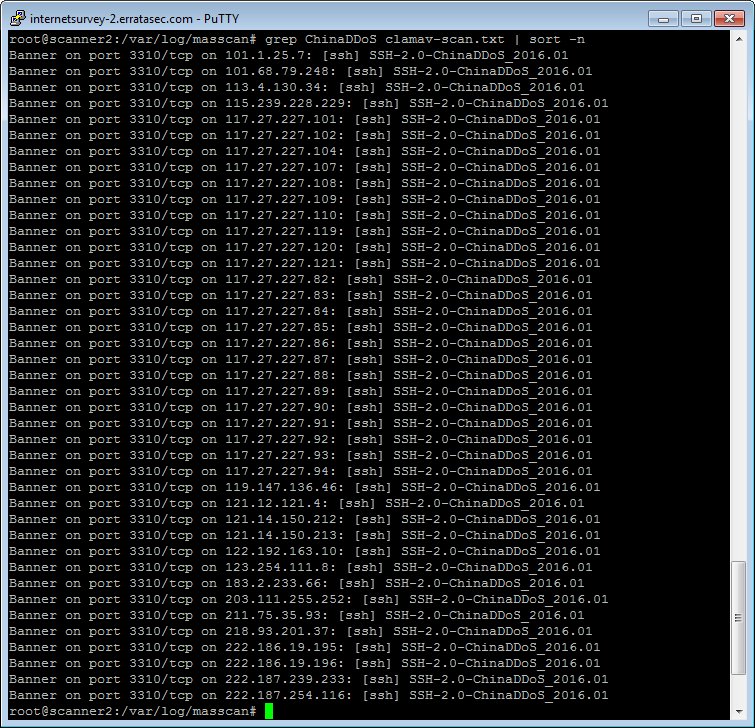
As for other things, I came across a bunch of systems claiming to be ChinaDDoS systems:
Conclusion
This sort of stuff shouldn't exist. The number of ClamAV systems available on the public Internet should be zero.
Even inside a corporate network, the number should be 0. If that stuff is turned on, then it should be firewalled (such as with iptables) so that only specific machines can access it.
Two important results are that half the systems are really old (EOLed, no longer supported), and only half the systems have the latest updates. There's some overlap -- systems with latest signature but out-of-date software.
...and then connects all the computers together.— Rob Graham ❄️ (@ErrataRob) June 14, 2016

Keep meaning to ask, what ISP do you use that allows you to do research scans? We'd like to do some, but obviously want abuse reports sent to usndirectly so we can remove IPs
ReplyDeleteVery informative post. I was not aware of this until I read this article. Thanks for sharing the information.
ReplyDeletePhD thesis writing
This comment has been removed by a blog administrator.
ReplyDeleteThis comment has been removed by a blog administrator.
ReplyDelete