Accidents vs. attack
The biggest flaw is that the comic confuses accidents vs. intentional attack. Airplanes and elevators are designed to avoid accidental failures. If that's the measure, then voting machine software is fine and perfectly trustworthy. Such machines are no more likely to accidentally record a wrong vote than the paper voting systems they replaced -- indeed less likely. The reason we have electronic voting machines in the first place was due to the "hanging chad" problem in the Bush v. Gore election of the year 2000. After that election, a wave of new, software-based, voting machines replaced the older inaccurate paper machines.
The question is whether software voting machines can be attacked. Well, if that's the measure, then airplanes aren't safe at all. Security against human attack consists of the entire infrastructure outside the plane, such as TSA forcing us to take off our shoes, to trade restrictions to prevent the proliferation of Stinger missiles.
Confusing the two, accidents vs. attack, is used here because it makes the reader feel superior. We get to mock and feel superior to those stupid software engineers for not living up to what's essentially a fictional standard of reliability.
To repeat: software is better than the mechanical machines they replaced, which is why there are so many software-based machines in the United States. The issue isn't normal accuracy, but their robustness against a different standard, against attack -- a standard which airplanes and elevators suck at.
The problems are as much hardware as software
Last year at the DEF CON hacking conference they had an "Election Hacking Village" where they hacked a number of electronic voting machines. Most of those "hacks" were against the hardware, such as soldering on a JTAG device or accessing USB ports. Other errors have been voting machines being sold on eBay whose data wasn't wiped, allowing voter records to be recovered.
What we want to see is hardware designed more like an iPhone, where the FBI can't decrypt a phone even when they really really want to. This requires special chips, such as secure enclaves, signed boot loaders, and so on. Only once we get the hardware right can we complain about the software being deficient.
To be fair, software problems were also found at DEF CON, like an exploit over WiFi. Though, a lot of problems are questionable whether the fault lies in the software design or the hardware design, fixable in either one. The situation is better described as the entire design being flawed, from the "requirements", to the high-level system "architecture", and lastly to the actual "software" code.
It's lack of accountability/fail-safes
We imagine the threat is that votes can be changed in the voting machine, but it's more profound than that. The problem is that votes can be changed invisibly. The first change experts want to see is adding a paper trail, rather than fixing bugs.
Consider "recounts". With many of today's electronic voting machines, this is meaningless, with nothing to recount. The machine produces a number, and we have nothing else to test against whether that number is correct or false. You can press a button and do an instant recount, but it won't tell you any other answer than the original one.
A paper trail changes this. After the software voting machine records the votes, it prints them to paper for the voter to check. This retains the features of better user-interface design than the horrible punch-hole machines of yore, and retains the feature of quick and cheap vote tabulation, so we know the results of the election quickly. But, if there's an irregularity, there exists an independent record that we can go back, with some labor, and verify.
It's like fail-systems in industrial systems, where we are less concerned about whether the normal systems have an error, but much more concerned about whether the fail-safe system works. It's like how famously Otis is not the inventor of elevators, but the inventor of elevator brakes that will safely stop the car from plummeting to your death if the cable snaps.
What's lacking in election machines therefore is not good or bad software engineering, but the failure of anybody to create fail-safes in the design, fail-safes that will work regardless of how the software works.
It's not just voting machines
It's actually really hard for the Russians to hack voting machines, as they have to be attacked them on a one-by-one basis. It's hard for a mass hack that affects them all.
It's much easier to target the back-end systems that tabulate the votes, which are more often normal computers connected to the Internet.
In addition, there are other ways that hackers can target elections. For example, the political divide in America between rural (Republican) and urban (Democrat) voters is well known. An attack against traffic lights, causing traffic jams, is enough to swing the vote slightly in the direction of rural voters. That makes a difference in places like last night's by-election in Ohio where a House candidate won by a mere 1,700 votes.
Voting machines are important, but there's way to much focus on them as if they are the only target to worry about.
Conclusion
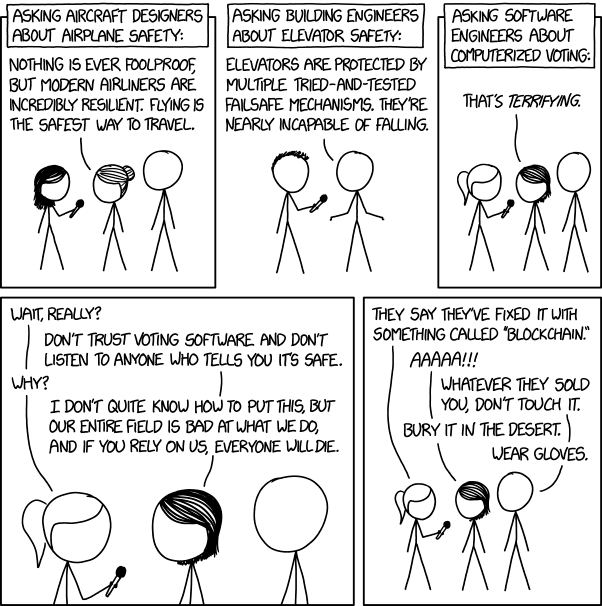
The humor of this comic rests on smug superiority. But it's wrong. It's applying a standard (preventing accidents) against a completely different problem (stopping attackers) -- software voting machines are actually better against accidents than the paper machines they replace. It's ignoring the problems, which are often more system and hardware design than software. It ignores the solution, which isn't to fix software bugs, but to provide an independent, auditable paper trail.
13 comments:
I still think that electronic voting is a bad idea in general. People need to trust the voting method, and you cannot trust machines. If you cannot be sure about the voting there's a demise in trust in basic democratic principles and we should not allow that.
Leaving the difference between accident and attack aside (which doesn't matter for the engineering part) you still don't know if the paper ballot is genuine. There would have to be some kind of unique marker, like a crypto-signed serial number or something similar, but there's the trust problem again. And there would be the need for 2 printed receipts: one for the voter to keep and one for the officials to keep for recounting. What if they differ?
All that aside I'm not sure that's what XKCD wants to express. This web comic usually has so many levels of humour maybe he wants exactly that: make us think about it. The (invisible) footnote about waiting for all researchers to have been retired gives it a totally new spin.
There's a wonderful novel about manipulating the german federal election with voting machines. Unfortunately it's in german and I'm not sure if Andreas Eschbach's book has already been translated to english (some of his books have). It's titled "A king for Germany", original title "Ein König für Deutschland". He elaborates voting systems and shows a clever way to forge voting machine software, even circumventing statistical methods to search for manipulations. Eschbach is a software developer himself and his novel is quite appealing. In the end the election is nullified and repeated when the plot is revealed but nevertheless all of it seems plausible to a very uncomfortable extent.
Yeah, people still have a irrational fear of computers, but, fun fact, most machines around us are actually software driven. Your toaster might not be, but your TV, or car engine, or even elevator certainly are. ATCs use computer assisted radars to guide air traffic, computers control power lines, water distribution systems, traffic lights, mobile networks etc., etc., and that's not even counting medical machines, or implantable devices like pacemakers or insulin pumps.
We literally trust software driven machines with our lives pretty much every day of our lives, but as soon as someone mentions voting machines, everyone else immediately goes "hell no, computers aren't reliable and can't be trusted"
Seems to me we're perfectly fine with computers we can't see, but fear the ones we can see...
I hope that the hovertext is there to explain that the author means "elevators and aircraft have 100 years of safety advances; voting machines can likewise be made reliable eventually." It's better than the more naïve/basic implication that "software is horrible" -- though unfortunately the latter is what I suspect most readers will take away.
But the "wait for them to retire" hovertext neglects advances made in many fields in the past 100 years, especially infosec, physical security, safety, and resilience engineering.
Aircraft and elevators have openly-published standards and every mis-action (whether 'accident' or 'attack', and whether an injury results or not) leads to review and usually revised standards for either construction or maintenance. That review is done not by the manufacturer but by a third party.
New medical procedures are likewise much safer than they might otherwise be because we are able to apply advances in the general practice of medicine. That those advances MUST be applied is again required and enforced by a third party.
For those who don't like the "big government" implication here, an open source standard (h/w and s/w) with contributions from experts in relevant fields, followed by a bug bounty type program, could certainly achieve good results in a handful of years -- addressing issues of both accuracy and public trust.
As others have pointed out elsewhere, folks will stop being dismissive of software engineering when practitioners (and their management/leadership) actually develop an active interest in continuous improvement together as an industry, like aviation and elevators.
For example, when the manufacturer of a voting machine pulls apart everything they did that led to a remote wifi vulnerability and educates the rest of the industry on how they got it wrong, and how to avoid getting that wrong again in future. Not high enough EAL? Let’s make EAL(>N) the new standard for voting machines. Couldn’t have secured wifi against unknown vulns within budget? Having wifi at all was the wrong choice. They fixed the flaw but machines weren’t updated? You know aircraft have this amazing new thing called airworthiness directives.... etc
The issue XKCD is mentioning is that currently any blockchain project is still effectively in a beta-phase. The blockchain advocates state that it's impossible to manipulate the blockchain because it would require at least 50% of all hashing-power and they simply state that this is not within the means of any nation state actor. In reality however, this is still unknown, but given the fact that 81% of all Bitcoin hashing-power is concentrated in China (source: https://www.buybitcoinworldwide.com/mining/pools/ ), I am willing to accept the possibility that any nation state actor could manipulate every arbitrary blockchain at will.
However, there is one issue which neither the author, nor the XKCD touches on, which is an absolute showstopper for any form of digital elections: (reasonable) voter anonymity. (Reasonable meaning provably prohibitively expensive, even for a nation state actor)
The requirement of reasonable voter anonymity even dominates the requirements of accurate registration of votes! The solution "add a paper trail" which is proposed by the experts, even further destroys the concept of voter anonymity, becuase the order in which the votes are cast, can be matched against external real world data such as CCTV footage, timestamped GPS-cooridnates from smartphones and other datasources which can effectively de-anonymize the voter. This scenario is not even far-fetched, because it happened in post-war Germany and it happens nowadays in Russia and various countries in Africa and the Middle-East.
The paper systems have a very, very high accuracy while lacking the other problems of voting machines (voter anonymity, trust, accuracy, manipulation from the outside, etc...). In my opinion, the machines need to do provably better on all these fronts combined, before we can throw out the paper ballots. Nowadays this simply is not the case and therefore I agree with the picture XKCD is sketching.
Are you kidding me?
The first thing you learn about security is that there is no real difference between an accidental and intentional attack… We have a huge history of incredibly efficient accidental attacks on IT systems.
NO...the problem with voting machines is not one of accidents vs intentional attacks.
The problem is that voting machines are not trustworthy, they seem to be designed to be intentionally hackable.
They are closed source, produced and promoted by commercial entities with unknown ownership, and promoted and supported by politicians with close ties to those same commercial entities.
Voting machines seem designed to be tools for manipulating elections, not just tabulating votes.
A non-corrupt country would develop open source voting machines that can be verified in the field.
The issue here is politics which means other government would be interested on interfering so the risk is way higher. No governments would be interested on taking a plan down or an elevator. The issue is the damage that it could lead to.
"software voting machines are actually better against accidents than the paper machines they replace."
I don't see how this assumption follows. It's immune to the specific problems that physical voting is, but there's fewer guarantees there isn't a buffer overflow, memory leak, or one of any number of other problems that could affect accuracy, intentional or not.
Isn't the entire point that other disciplines take care to actually develop systems that are testable to be free of known defect classes? Airplanes and bridges still clearly have a surface that a malicious person could do something with, but have a far better track record for doing what their specification says they are supposed to do without catastrophic failure. Whether the tone of XKCD makes you butthurt or not, software is inarguably behind in that regard.
I feel it is this article, NOT XKCD that is wrong here. Each device must protect against the primary sources of threat to those systems. For an elevator it is an accident, for a voting machine it is an intentional attack.
So we do need to throw away voting machines that are not resistant to explicit attack, while (at least so far) we can live with Elevators that are not resistant to attack.
The other difference is accountability. If you use an elevator and you arrived safely, you know that all is well, no issues with accountability. If you had an election and someone what elected, you have no idea if all is well.
XKCD is right. we have along way to go, before we have effective electronic voting machines.
I think you are missing distinctions that matter here.
--dan
Regarding the difference between accidents and intentional attack, I think you're missing the point. It's a fundamental part of the requirements around voting that the system be protected against attacks, and not just small attacks - large, coordinated and well-resourced attacks. In truth, there are requirements for airplanes and elevators to be resistant against this sort of attack, but they're nowhere near the top of the list. This is in sharp contrast to voting, where resistance to this type of attack is key.
I think that's why the XKCD comic has so many supporters.
But you're clearly right about the need for the need for a good set of requirements that include the need for fail safes, and that it should cover the entire system. I think it's more than that though - we should be listing the threats we're concerned about and our level of concern. Ideally any solution would be judged against how well they both meet the explicit requirements and are resistant to threats. Part of the reason people seem to argue at cross-purposes a lot when it comes to voting machines is a lack of any agreement about what threats the entire voting system needs to resilient against.
Regarding paper trails, while this would meet some of the requirements, most models I've seen don't give the voter the chance to verify that the vote they've just cast is correct. IMHO yet another win for paper voting.
> And there would be the need for 2 printed receipts: one for the voter to keep and one for the officials to keep for recounting. What if they differ?
This is pretty simple to solve. The machine prints both receipts for the voter. The voter compares the two receipts to make sure they match, then submits one for the record and keeps the other.
> For those who don't like the "big government" implication here, an open source standard (h/w and s/w) with contributions from experts in relevant fields, followed by a bug bounty type program, could certainly achieve good results in a handful of years -- addressing issues of both accuracy and public trust.
I agree with this. Philosophically speaking, democracy in the USA is built on the concept of sovereignty of the people--not the government and certainly not Diebold. The people express their consent/opinion through voting, so the power to examine our election systems in full detail is an absolute requirement. Otherwise, you can end up with a situation like North Korea, that "democratically" always elects Kim Jong-un, with 100% of the vote.
Thanks for sharing such a useful and informative post like this. Keep updating more updates like this.
Equity Tips
Post a Comment